In an era defined by data-driven decision making, organizations face an escalating dilemma: how to extract value from sensitive data without exposing it to risk. Healthcare providers manage confidential patient records, financial institutions process highly sensitive transaction histories, and governments safeguard critical citizen information. At the same time, artificial intelligence and advanced analytics demand large and diverse datasets. Privacy-preserving computation tools such as OpenMined are emerging as essential solutions, enabling collaboration and innovation without sacrificing confidentiality.
TLDR: Privacy-preserving computation tools like OpenMined allow organizations to analyze and learn from sensitive data without directly accessing or exposing it. Using techniques such as federated learning, secure multiparty computation, and differential privacy, these tools reduce the risks associated with centralized data storage. They are increasingly vital for industries handling personal, financial, and medical information. By combining advanced cryptography with practical engineering frameworks, they help reconcile innovation with strict privacy requirements.
Modern data ecosystems are complex and interconnected. Enterprises aggregate information from mobile applications, IoT devices, cloud services, and internal systems. Traditionally, analytics required centralizing this data into large repositories. While effective for modeling, this approach creates significant vulnerabilities, including:
- Single points of failure that attract malicious actors.
- Compliance risks under regulations such as GDPR, HIPAA, and CCPA.
- Insider threats from unauthorized access or misuse.
- Public trust erosion in the event of breaches.
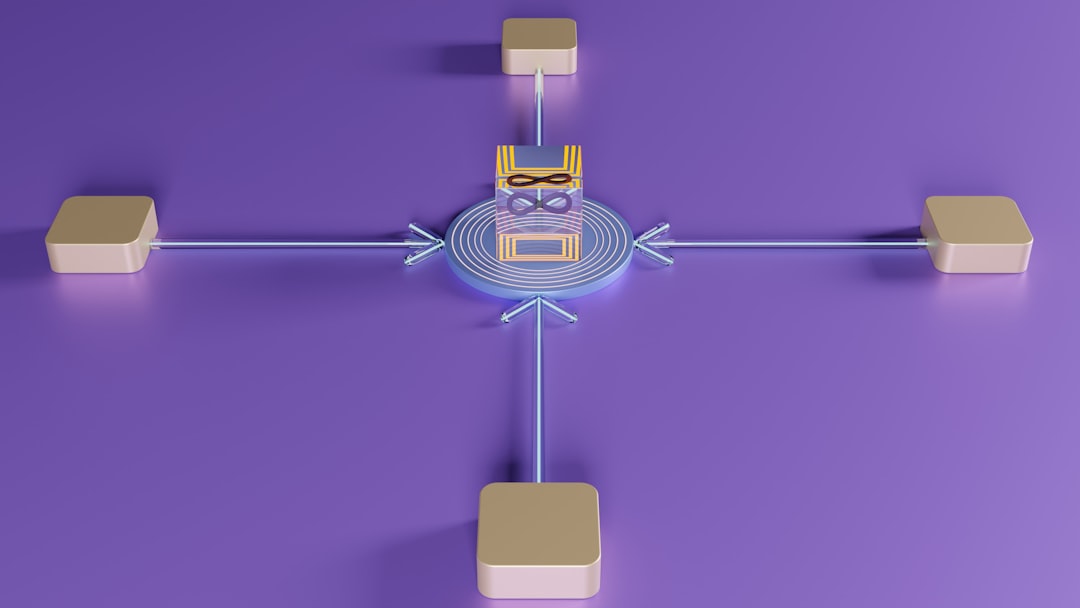
Privacy-preserving computation changes the paradigm. Rather than bringing data to the model, organizations can bring the model to the data. Computation occurs locally or in encrypted form, and only aggregated, privacy-protected results are shared. This shift transforms how institutions collaborate while maintaining data sovereignty.
Understanding OpenMined and Its Mission
OpenMined is an open-source community and ecosystem focused on making privacy-preserving AI accessible and practical. It provides tools, libraries, and educational resources that enable developers and enterprises to train models and compute on sensitive datasets without directly exposing raw information.
At its core, OpenMined promotes a vision where privacy and utility are not mutually exclusive. By building infrastructure around encrypted computation and decentralized learning, it seeks to ensure that AI development respects individual rights and organizational compliance requirements.
The ecosystem typically integrates with popular machine learning frameworks and enables:
- Federated model training across distributed datasets.
- Secure multiparty computation for joint analysis.
- Differential privacy to limit re-identification risks.
- Encrypted inference to protect model inputs and outputs.
Core Technologies Behind Privacy-Preserving Computation
1. Federated Learning
Federated learning allows multiple participants—such as hospitals, banks, or mobile devices—to collaboratively train a machine learning model without transferring their underlying datasets. Instead, each participant:
- Downloads a shared model.
- Trains it locally on private data.
- Sends encrypted or aggregated model updates back to a central coordinator.
The coordinator merges updates to improve the global model. Raw data never leaves its original location. This dramatically reduces exposure risk and supports regulatory compliance.
Use case example: A group of hospitals can collaboratively train a cancer detection model using patient scans without sharing any individual medical records.
2. Secure Multiparty Computation (SMPC)
Secure multiparty computation allows several parties to compute a function over their inputs while keeping those inputs private. Each participant contributes encrypted fragments of data. The system ensures that no single party can reconstruct another’s dataset.
This is particularly powerful for financial institutions or research consortia seeking joint insights without compromising competitive or confidential information.
Key benefits include:
- Mathematical guarantees of confidentiality.
- Elimination of the need for a trusted central authority.
- Reduced legal exposure when sharing insights.
3. Differential Privacy
Differential privacy introduces controlled statistical noise into outputs, ensuring that no single individual’s data significantly influences the result. Even if an attacker analyzes the output, they cannot reliably infer whether a specific individual’s information was included.
This method provides quantifiable privacy assurances and is increasingly recognized by regulators as a robust protective measure.
4. Homomorphic Encryption
Homomorphic encryption enables computations to be performed directly on encrypted data. The results, when decrypted, match the output as if the computation had occurred on plaintext.

Although computationally intensive, advances in cryptography are steadily improving performance. For highly sensitive datasets, the additional overhead is often justified by the enhanced security profile.
Why These Tools Matter in Regulated Industries
Privacy-preserving computation is not merely a technical innovation; it is becoming a strategic necessity. Consider the following sectors:
Healthcare
Patient confidentiality is both an ethical and legal imperative. Federated learning enables collaborative research across institutions without transmitting identifiable health records. This accelerates medical breakthroughs while respecting privacy mandates.
Finance
Banks and financial technology companies must protect transaction data and personal financial histories. Secure multiparty computation allows anti-fraud models to be trained across institutions without revealing proprietary datasets.
Government and Public Sector
Public agencies often hold sensitive demographic and security information. Privacy-preserving frameworks support analytics for public policy planning without exposing detailed citizen data.
Technology Platforms
Consumer-facing platforms must balance personalization with privacy expectations. On-device model training and encrypted inference reduce reliance on centralized data harvesting.
Operational and Strategic Advantages
Organizations adopting tools like OpenMined gain more than compliance benefits. They position themselves for sustainable, trust-centered growth.
Operational benefits include:
- Reduced data breach surface area.
- Lower liability exposure.
- Alignment with evolving privacy regulations.
- Enhanced resilience against insider threats.
Strategic benefits include:
- Strengthened brand trust and reputation.
- Increased willingness from partners to collaborate.
- Improved customer confidence.
- Future-proofed data governance frameworks.

Challenges and Considerations
Despite their advantages, privacy-preserving computation tools are not without limitations. Organizations must approach implementation with careful planning.
Common challenges include:
- Performance overhead: Cryptographic operations can increase computational demands.
- Technical complexity: Specialized expertise is often required for deployment and maintenance.
- Interoperability concerns: Integrating with legacy systems may require architectural changes.
- Governance alignment: Internal policies must adapt to decentralized data models.
A realistic adoption strategy involves phased implementation, pilot projects, and cross-functional collaboration between data scientists, cybersecurity teams, and compliance officers.
Building a Responsible Data Future
As artificial intelligence continues to evolve, the demand for diverse and high-quality datasets will only intensify. However, society’s tolerance for invasive data practices is diminishing. Regulators are imposing stricter controls, and individuals are increasingly aware of how their personal information is used.
Privacy-preserving computation offers a principled path forward. By embedding cryptographic safeguards into the analytical process itself, tools like OpenMined create an environment where innovation does not depend on secrecy or risk.
Importantly, these technologies encourage a new mindset: data minimization and decentralization by design. Instead of accumulating vast centralized repositories, organizations distribute computation, limit exposure, and apply mathematical guarantees to protect participants.
This approach aligns with broader cybersecurity trends emphasizing zero trust architectures, encryption-by-default, and privacy-first engineering.
Conclusion
Privacy-preserving computation tools such as OpenMined represent a meaningful advancement in secure data science. By leveraging federated learning, secure multiparty computation, differential privacy, and homomorphic encryption, these frameworks reconcile the need for advanced analytics with growing privacy obligations.
For organizations handling sensitive data, adopting such tools is not merely a technological upgrade; it is a strategic investment in resilience, compliance, and public trust. As data ecosystems expand and cyber threats grow more sophisticated, protecting sensitive information must be embedded into the computation process itself.
The future of AI and data analytics depends on trust. Privacy-preserving technologies provide the technical and ethical foundation necessary to sustain that trust while enabling responsible innovation.

